Member-only story
GCP IAM Authentication and Authorization 101
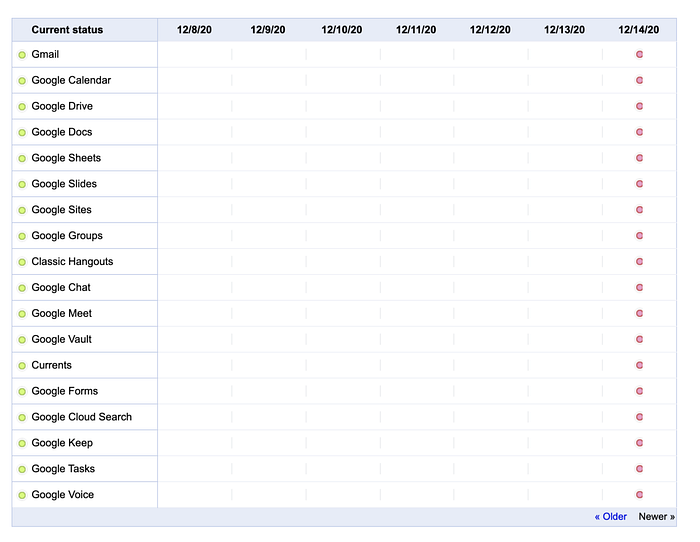
Just a few days ago, on 14th Dec., Google IAM experienced a 50-minute outage🔥 and resulted in the unavailability of all the user verification services that rely on it worldwide. Youtube alone lost 1.7 million💸 in advertising revenue, while the losses of other websites were utterly incalculable.
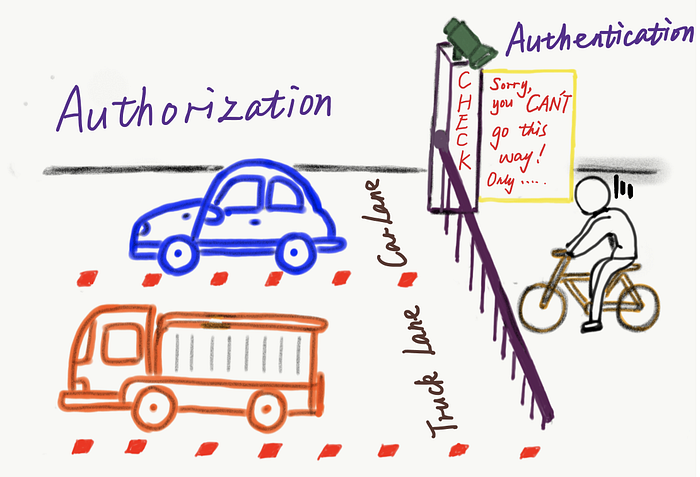
- What is Google IAM?
- Why does this matter so much?
- How much do you know about Authentication and Authorization on GCP?
- How do you align GCP IAM with Kubernetes RBAC?
What’s a User
Traditional web systems often have independent user designs, storing data containing basic user information, such as ages, names, birthdays, emails, phone numbers, etc., in the database. The most important data is user passwords, using which users log in to the website after inputting the username.
There are a wider variety of users in the cloud era, though the user definition has not changed much. Google users are no longer limited to Google only. Many websites have integrated Google’s third-party login now, and by obtaining the users’ basic information after user authorization, they enable users to log in directly.

It brings much convenience.
- It is no longer required to build an independent user management system. Relying on a giant like Google and its huge user base, you can save resources and expand the users’ scope.
- Reduce security vulnerabilities. The data leakage on the Internet and its consequences of losing user information are not rare. Meanwhile, the loss caused by the imprudent management of ordinary user passwords (59% of users always use the same set of passwords) is unpredictable.
- The authenticity and validity of user information are higher. The reliability of Google account information is generally assumed to be much higher than many websites(users tend to fill in false…